Difference between revisions of "Firewalls"
Views
Actions
Namespaces
Variants
Tools
imported>Dalto m (Dalto moved page UFW & GUFW to Firewalls: Generalize) |
imported>Dalto (Revamp page and content) |
||
| Line 1: | Line 1: | ||
__TOC__ | __TOC__ | ||
=Overview= | |||
Running a local firewall is almost always a good practice. Even when you are behind a network firewall, a local firewall protects you from threats on the inside of your network. | |||
=UFW= | |||
UFW stands for Uncomplicated FireWall, and is a program for managing a netfilter firewall. It provides a command line interface and aims to be uncomplicated and easy to use. UFW is far simpler than iptables and a good place to start unless you have very specialized needs. | |||
==Installing UFW== | |||
You can install the {{ic|ufw}} package using you favorite package manager or the command: | |||
pamac install ufw | |||
Once UFW is installed you need to start and enable it using the commands: | |||
sudo systemctl enable ufw.service | |||
sudo ufw enable | |||
{{warning|Don't enable both iptables.service and ufw.service}} | |||
==Adding Rules== | |||
To view the current configuration you can use the command {{ic|ufw status}}. Here is what it looks like in a new install: | |||
<pre> | |||
sudo ufw status verbose | |||
Status: active | |||
Logging: on (low) | |||
Default: deny (incoming), allow (outgoing), disabled (routed) | |||
New profiles: skip | |||
</pre> | |||
This indicates that it will block all incoming traffic and allow all outgoing traffic. This is a good starting point for most desktop systems. However, often we will want to allow some incoming traffic. This can be done with the command {{ic|ufw allow}}. For example, if we want to allow incoming ssh traffic so we can connect to the machine from other machines on the network we could use the command: | |||
sudo ufw allow ssh | |||
sudo | If we wanted to also tcp connections to a local webserver on a non-standard https port, 8443. We could use the command: | ||
sudo ufw allow in 8443/tcp | |||
{{ | {{tip|When you don't specify "in" or "out", "in" is assumed}} | ||
==UFW and Applications== | |||
You may notice a difference in the above two commands. When we built the rules for ssh we used the name and for https we used the port number, 8443. This is because UFW has a small database of applications it knows the ports for. You can see the list with the command: | |||
sudo ufw app list | sudo ufw app list | ||
sudo | For applications on the list you can add them by name. If you want to review the configuration for one of the applications, you can use the command {{ic|ufw app info}}. For example, to the configuration for ssh: | ||
<pre>sudo ufw app info SSH | |||
Profile: SSH | |||
Title: SSH server | |||
Description: SSH server | |||
Port: | |||
22/tcp | |||
</pre> | |||
= GUFW = | {{tip|When using ufw app the commands are case sensitive but when adding rules they are not}} | ||
Some additional preconfigured applications can be added by installing the package {{ic|ufw-extras}} with your favorite package manager or the command: | |||
pamac install ufw-extras | |||
==Removing Rules== | |||
Rules can be removed with the {{ic|ufw delete}} command. For example, to delete our 8443 rules we could use the command: | |||
sudo ufw delete allow 8443/tcp | |||
You can also delete them by number. This is easier if you have a numbered list which you can see with the command: | |||
<pre> | |||
sudo ufw status numbered | |||
Status: active | |||
To Action From | |||
-- ------ ---- | |||
[ 1] 22 ALLOW IN Anywhere | |||
[ 2] 22 (v6) ALLOW IN Anywhere (v6)</pre> | |||
Now if we wanted to stop allowing ssh on ipv6 we could use the command: | |||
sudo ufw delete 2 | |||
==GUFW== | |||
[[File:gufw.jpg|thumb|left|240px]] | [[File:gufw.jpg|thumb|left|240px]] | ||
GUFW is a GTK front-end for | Prefer to use GUI applications and still want to manage your firewall? No problem. GUFW is a GTK front-end for UFW that aims to make managing a Linux firewall as accessible and easy as possible. It features pre-sets for common ports and p2p applications. | ||
If it is not installed already gufw can be installed from the repos: | If it is not installed already gufw can be installed from the repos: | ||
pamac install gufw | |||
It will now be available in the menu as '''Firewall Configuration''' or by running {{ic|gufw}} directly. | |||
<div style="clear: both"></div> | |||
=See Also= | |||
* The Arch Wiki on [https://wiki.archlinux.org/index.php/Ufw UFW] | |||
* The [https://help.ubuntu.com/community/UFW UFW website] | |||
* The [http://gufw.org/ GUFW website] | |||
[[Category:Contents Page]] | [[Category:Contents Page]] | ||
Revision as of 01:04, 27 May 2019
Overview
Running a local firewall is almost always a good practice. Even when you are behind a network firewall, a local firewall protects you from threats on the inside of your network.
UFW
UFW stands for Uncomplicated FireWall, and is a program for managing a netfilter firewall. It provides a command line interface and aims to be uncomplicated and easy to use. UFW is far simpler than iptables and a good place to start unless you have very specialized needs.
Installing UFW
You can install the ufw package using you favorite package manager or the command:
pamac install ufw
Once UFW is installed you need to start and enable it using the commands:
sudo systemctl enable ufw.service sudo ufw enable
Adding Rules
To view the current configuration you can use the command ufw status. Here is what it looks like in a new install:
sudo ufw status verbose Status: active Logging: on (low) Default: deny (incoming), allow (outgoing), disabled (routed) New profiles: skip
This indicates that it will block all incoming traffic and allow all outgoing traffic. This is a good starting point for most desktop systems. However, often we will want to allow some incoming traffic. This can be done with the command ufw allow. For example, if we want to allow incoming ssh traffic so we can connect to the machine from other machines on the network we could use the command:
sudo ufw allow ssh
If we wanted to also tcp connections to a local webserver on a non-standard https port, 8443. We could use the command:
sudo ufw allow in 8443/tcp
UFW and Applications
You may notice a difference in the above two commands. When we built the rules for ssh we used the name and for https we used the port number, 8443. This is because UFW has a small database of applications it knows the ports for. You can see the list with the command:
sudo ufw app list
For applications on the list you can add them by name. If you want to review the configuration for one of the applications, you can use the command ufw app info. For example, to the configuration for ssh:
sudo ufw app info SSH Profile: SSH Title: SSH server Description: SSH server Port: 22/tcp
Some additional preconfigured applications can be added by installing the package ufw-extras with your favorite package manager or the command:
pamac install ufw-extras
Removing Rules
Rules can be removed with the ufw delete command. For example, to delete our 8443 rules we could use the command:
sudo ufw delete allow 8443/tcp
You can also delete them by number. This is easier if you have a numbered list which you can see with the command:
sudo ufw status numbered
Status: active
To Action From
-- ------ ----
[ 1] 22 ALLOW IN Anywhere
[ 2] 22 (v6) ALLOW IN Anywhere (v6)
Now if we wanted to stop allowing ssh on ipv6 we could use the command:
sudo ufw delete 2
GUFW
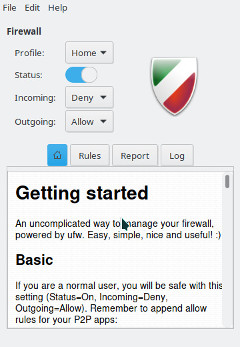
Prefer to use GUI applications and still want to manage your firewall? No problem. GUFW is a GTK front-end for UFW that aims to make managing a Linux firewall as accessible and easy as possible. It features pre-sets for common ports and p2p applications.
If it is not installed already gufw can be installed from the repos:
pamac install gufw
It will now be available in the menu as Firewall Configuration or by running gufw directly.
See Also
- The Arch Wiki on UFW
- The UFW website
- The GUFW website